Engineers Keep Smart City Systems Secure From Cyber Attacks
By utilizing interconnected technology, Smart Cities improve the lives of their citizens. The increased reliance on digital technologies and interconnected systems also exposes critical infrastructures to cyber threats.
 As more of the world’s population is predicted to move to urban environments, Smart Cities have emerged as a transformative solution to address energy efficiency, resource management, and urban development. The promise of Smart Cities is that they utilize technology to help reduce reliance on limited resources while improving the lives of their citizens and reducing carbon emissions.
As more of the world’s population is predicted to move to urban environments, Smart Cities have emerged as a transformative solution to address energy efficiency, resource management, and urban development. The promise of Smart Cities is that they utilize technology to help reduce reliance on limited resources while improving the lives of their citizens and reducing carbon emissions.
Smart cities leverage the convergence of the physical and cyber worlds. The interconnected IoT (Internet of Things) devices and data-driven systems optimize various physical urban functions. The increased reliance on digital technologies and interconnected systems also exposes these critical infrastructures to increased cyber threats. Robust cybersecurity measures are becoming indispensable in safeguarding Smart Cities and their citizens who rely on them.
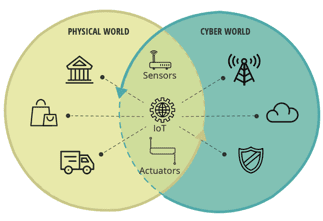
Source: Making smart cities cybersecure: Ways to address distinct risks in an increasingly connected urban future. A report from the Deloitte Center for Government Insights (n.d.).
There are two fundamental aspects of concern when it comes to security in a Smart City. The first is around data collection from its citizens. Smart Cities involve measuring people’s behavior in one way or another. From electricity usage to driving patterns, this data can be used to make the city work more efficiently and thereby reduce its carbon emissions. But it can come at the price of privacy. What data is being collected, and are the citizens even aware that data is being gathered?
Research on privacy preservation is ongoing. In their paper “Privacy-preserving Data Federation for Trainable, Queryable, and Actionable Data[1],” presented at the 2023 IEEE International Conference on Data Engineering Workshops (ICDEW), the authors introduce a privacy-preservation query engine that is able to efficiently align and aggregate decentralized data for more accurate results.
Controlling access to the systems that are managing the city is another critical aspect of managing cybersecurity in Smart Cities. For instance, attackers can wreak havoc by taking control of transportation systems or the energy grid, or any number of intelligent systems. One survey reports that ransomware attacks on local governments have increased from 34% in 2020 to 59% in 2021. The smarter the city, the greater the risk of attack.
In April 2023, cybersecurity agencies from the US, United Kingdom, Canada, Australia, and New Zealand issued a joint guide on Smart City best practices that provides an overview of risks to Smart Cities, including interconnected attack surfaces, information and communications technologies (ICT) supply-chain risks, and increased automation of infrastructure operations. To protect against these risks, the guide offers three recommendations to help communities strengthen their cyber posture: secure planning and design, proactive supply-chain risk management, and operational resiliency.
Common Cybersecurity Threats in Smart Cities
Proactive Measures to Mitigate Cybersecurity Threats
|
Standard controls such as utilizing strong passwords and two factor authentication along with strong monitoring systems can help keep systems safe. Advances in real-time detection of cyberattacks show promise in blocking attackers from entering the systems at the moment they are detected.
In their paper “Cybersecurity-Enhanced Encrypted Control Systems Using Keyed-Homomorphic Public Key Encryption[2],” published in IEEE AccessⓇ, the authors propose a cyberattack-detectable encrypted control system.
Cybersecurity control systems often need to be deployed within an aging infrastructure of computing systems. There are challenges with keeping computing systems current, whether it is the hardware or software. In January 2023, IEEE published the IEEE P1547 Draft Guide for Cybersecurity of Distributed Energy Resources Interconnected with Electric Power Systems[3] as guidance for cybersecurity for distributed energy resources that are connected with electric power systems such as fuel cells, photovoltaics, wind turbines, and other distributed energy resources.
As urban environments increasingly rely on technology to support their carbon-emission plans, it is critically important to keep the city’s citizens and systems safe. A recently published article in IEEE Transmitter, Smart Cities 2030: How Tech is Reshaping Urbanscapes, describes Smart Cities today and in 2030, highlighting technologies as well as the IEEE members actively engaged in these developments. It’s just one example of how IEEE provides many resources to stay current on the technologies that will shape our future.
[1] S. Iatropoulou, T. Anastasiou, S. Karagiorgou, P. Petrou, D. Alexandrou and T. Bouras, “Privacy-preserving Data Federation for Trainable, Queryable and Actionable Data,” 2023 IEEE 39th International Conference on Data Engineering Workshops (ICDEW), Anaheim, CA, USA, 2023, pp. 44-48, doi: 10.1109/ICDEW58674.2023.00012.
[2] M. Miyamoto, K. Teranishi, K. Emura and K. Kogiso, “Cybersecurity-Enhanced Encrypted Control System Using Keyed-Homomorphic Public Key Encryption,” in IEEE Access, vol. 11, pp. 45749-45760, 2023, doi: 10.1109/ACCESS.2023.3274691.
[3] IEEE Draft Guide for Cybersecurity of Distributed Energy Resources Interconnected with Electric Power Systems, in IEEE P1547.3/D3.11, January 2023, pp.1-158, 13 February 2023.